Payroll Data Security and Access Controls

Comprehensive Guide to Payroll Data Security and Access Controls for Ensuring Compliance and Protecting Employee Information
By Josh Henderson, Denali HR
Payroll data security is a critical priority for organizations of every size in light of rising breaches and cyber threats. This guide outlines the practices and access controls required to protect sensitive payroll information while maintaining regulatory compliance. It explains protection mechanisms, access control models, and best practices to preserve data integrity. Given the dual requirement to protect employee information and meet compliance obligations, these topics are essential. The article addresses payroll compliance best practices, access control models, techniques to secure payroll data, the role of outsourced HR partners, and tools that strengthen payroll software security.
Traditional payroll systems frequently encounter notable challenges in security, transparency, and compliance, increasing their susceptibility to fraud and breaches.
Blockchain for Payroll Data Security & Compliance
Organizations in the global economy face substantial challenges in payroll operations, especially regarding data security, transparency, and compliance with diverse regulatory standards. Traditional, centralized payroll systems are vulnerable to fraud, inefficiency, and increased operational costs. These systems introduce risks such as unauthorized data access and single points of failure, which can lead to data breaches and financial loss.
Ensuring Privacy and Data Integrity in Payroll Systems Using Blockchain and IPFS, R Lenka, 2025
What Are the Essential Payroll Compliance Best Practices for Data Security?
Payroll compliance requires following applicable regulations and adopting practices that protect employee data. Core actions include accurate payroll tax filings, correct employee classification, and maintaining comprehensive documentation. These measures reduce the risk of penalties and strengthen payroll data security. A robust compliance framework helps mitigate breach risks and keeps employee information confidential.
How Do Regulatory Requirements Impact Payroll Data Protection?
Regulatory obligations shape payroll data protection strategies. Laws such as the Fair Labor Standards Act (FLSA) and the Health Insurance Portability and Accountability Act (HIPAA) require businesses to implement specific security safeguards for employee data. Non-compliance can result in substantial fines and legal consequences. Therefore, familiarity with relevant statutes is essential to design effective payroll protection.
Which Steps Ensure Ongoing Payroll Compliance and Risk Reduction?
Maintaining ongoing payroll compliance and reducing risk requires proactive measures. Implement regular compliance audits, provide continuous employee training on data security, and deploy structured HR systems for accurate record-keeping. Cultivating a culture of compliance and vigilance lowers breach risk and keeps payroll processes secure.
How Do Access Control Models Secure Payroll Systems Effectively?
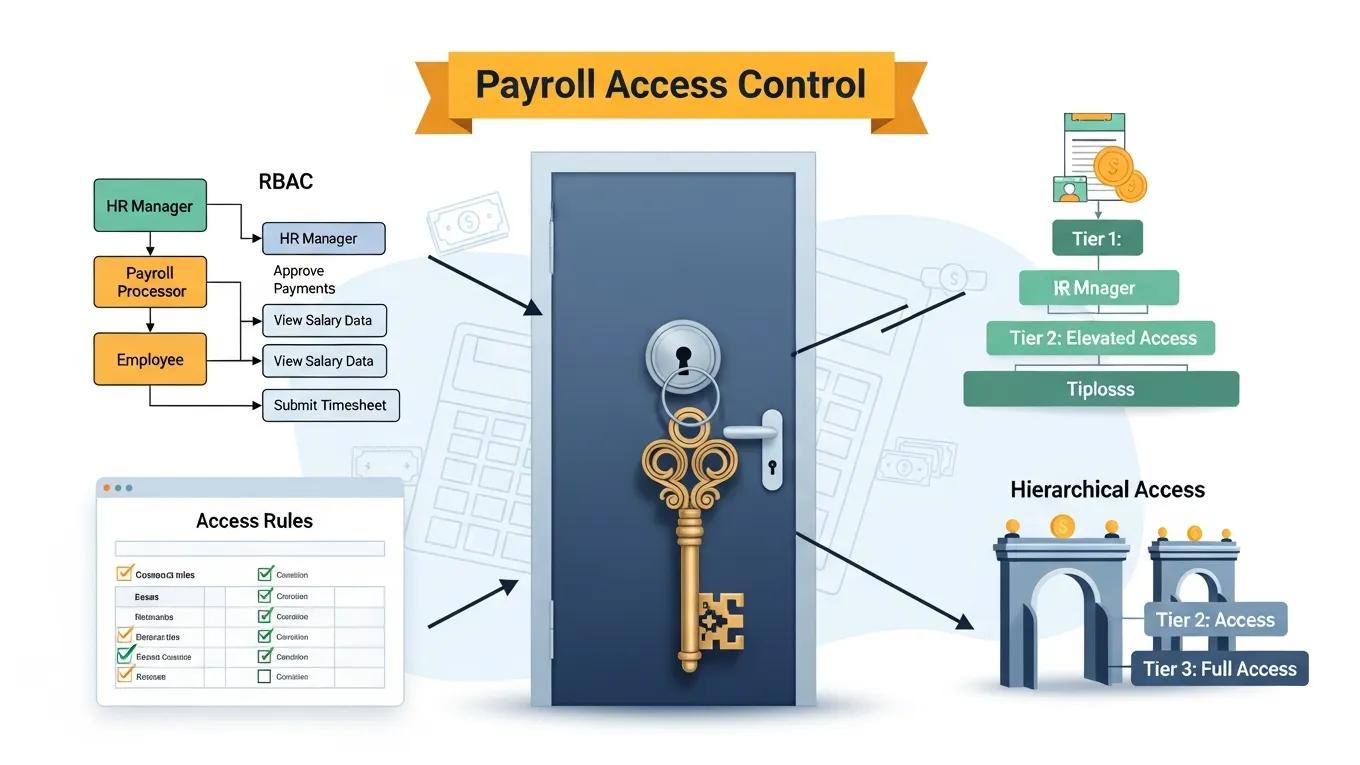
Access control models secure payroll systems by defining who may access sensitive data and under what conditions. Effective controls prevent unauthorized access and limit exposure to breaches. Common models—role-based (RBAC), mandatory (MAC), and discretionary (DAC)—offer different balances of security and operational flexibility.
What Is Role-Based Access Control and Its Benefits in Payroll Security?
Role-based access control (RBAC) restricts system access according to employees’ organizational roles. RBAC ensures users access only the information required for their duties, reducing unauthorized access and simplifying access administration. Implemented correctly, RBAC strengthens payroll security and lowers breach likelihood.
How Does Multi-Factor Authentication Enhance Payroll Access Management?
Multi-factor authentication (MFA) strengthens payroll access by requiring two or more verification factors before granting access to sensitive data. MFA substantially reduces the risk of compromised accounts and, when integrated into payroll systems, improves the organization’s security posture to better protect employee information.
What Are the Best Practices for Protecting Employee Payroll Data?
Protecting payroll data combines technology and governance. Implement data encryption, perform regular audits, and train employees on security protocols. Together, these measures reduce exposure to unauthorized access and potential breaches.
How Is Data Encryption Used to Safeguard Payroll Information?
Data encryption converts sensitive payroll information into unreadable ciphertext that only authorized parties can decrypt. Encryption protects data in transit and at rest, reducing the impact of interception and preserving confidentiality and integrity.
Recent research highlights the need for advanced, AI-optimized approaches to protect data in complex HR and payroll integrations.
AI-Optimized Security for HR & Payroll Data Exchange
The secure transfer of HR data between cloud-based human capital management platforms and downstream payroll systems is a major enterprise concern as organizations adopt distributed integration architectures. The study evaluates confidentiality, integrity, and exposure risks in data flows between SAP SuccessFactors and payroll platforms, focusing on personally identifiable and financial information that is subject to strict regulation. It concludes that perimeter-based security and static encryption alone do not prevent overexposure, misuse, or operational leakage of sensitive HR attributes during routine payroll processing. The paper proposes a unified control framework combining strong cryptographic protection, policy-driven masking, strict data minimization, and AI-optimized decision logic tailored to current technology
Secure HR Data Exchange between SAP SuccessFactors and Payroll Using AI-Optimized Encryption, Masking, and
Data Minimization Controls, M Parasa, 2026
Why Are Audit Trails and Monitoring Critical for Payroll Security?
Audit trails and monitoring are essential for payroll security. They record access and changes to sensitive data, enabling detection of unauthorized attempts and potential breaches. Regular review of audit logs strengthens security controls and supports regulatory compliance.
How Do Outsourced HR Partners Enhance Payroll Security and Compliance?

Outsourced HR partners enhance payroll security and compliance by providing specialist expertise and dedicated resources. They implement robust controls, automate payroll workflows, and maintain compliance, enabling organizations to focus on core activities while preserving secure payroll operations.
What Security Protocols Do Outsourced Payroll Services Implement?
Outsourced payroll providers typically deploy multiple security protocols such as data encryption, strict access controls, and scheduled security audits. Leveraging external expertise helps organizations improve payroll security and maintain regulatory compliance.
How Does Partnering with Denali HR Simplify Payroll Data Protection?
Partnering with Denali HR centralizes payroll protection through integrated support services that prioritizes compliance, risk mitigation, and efficient employee administration. Denali HR provides secure payroll processing, onboarding, and documentation management to simplify handling of sensitive payroll data with robust access controls.
Which Tools and Software Features Improve HR Payroll Software Security?
Several tools and software features improve HR payroll security. Key capabilities include data encryption, secure access controls, and compliance management modules. These tools help organizations protect payroll information and meet regulatory obligations.
What Payroll Software Security Features Are Essential for Access Control?
Effective payroll software includes security features that support access control, such as role-based access, audit trails, and multi-factor authentication. Combining these features creates a controlled environment for payroll data and reduces risk of unauthorized access.
How Do Secure Employee Payroll Systems Integrate Compliance and Access Management?
Secure payroll systems combine compliance and access management by centralizing HR documentation and tracking compliance metrics. This integration enables efficient handling of sensitive payroll data while ensuring adherence to regulatory requirements and streamlining payroll workflows.
How Can Businesses Prevent Payroll Fraud Through Effective Access Controls?
Preventing payroll fraud requires proactive access controls and continuous monitoring. Establishing clear access management protocols helps reduce fraudulent activity and protect employee data.
What Are Common Payroll Fraud Risks and How to Mitigate Them?
Common payroll fraud risks include unauthorized system access, data manipulation, and identity theft. Mitigation measures include robust access controls, routine audits, and employee training to recognize fraudulent behaviour. A culture of vigilance strengthens protection of payroll systems.
Which Access Management Practices Reduce Payroll Fraud Incidents?
Access practices that reduce payroll fraud include role-based access control, segregation of duties, and periodic access reviews. Limiting employee access to only what is necessary for their role reduces fraud risk and improves overall payroll security.
Frequently Asked Questions
What are the consequences of non-compliance with payroll data regulations?
Non-compliance can result in substantial fines, legal penalties, and reputational harm. Regulatory enforcement may trigger audits and investigations, and affected employees can pursue litigation that increases financial exposure. Maintaining compliance protects the organization and preserves trust with employees and stakeholders.
How can businesses assess their payroll data security risks?
Assess risk through comprehensive evaluations that review current controls, identify vulnerabilities, and analyze potential threats. Examine access controls, encryption practices, and training programmes. Consider engaging third-party security experts for audits and penetration testing. Update assessments regularly to address emerging threats.
What role does employee training play in payroll data security?
Employee training is essential to payroll data security. Regular sessions covering phishing, secure password practices, and data confidentiality reduce human error—the leading cause of breaches. Trained staff are more likely to follow protocols and report suspicious activity.
How can businesses ensure the effectiveness of their access control measures?
Ensure effectiveness by regularly updating access policies to reflect role changes and by applying the principle of least privilege. Conduct periodic audits of access logs and user permissions to detect unauthorized activity. Continuous monitoring and adaptation to new threats improve control effectiveness.
What technologies can enhance payroll data security?
Technologies that strengthen payroll security include advanced encryption, multi-factor authentication (MFA), and secure cloud storage. Encryption protects data by rendering it unreadable, MFA requires multiple verification factors, and secure cloud services offer resilient data protection and support compliance.
How can organizations measure the success of their payroll security initiatives?
Measure success with KPIs such as security incident counts, compliance audit outcomes, and employee training completion rates. Regularly review these metrics to identify improvement areas. Employee surveys on awareness and adherence can also gauge the organisation’s security culture.